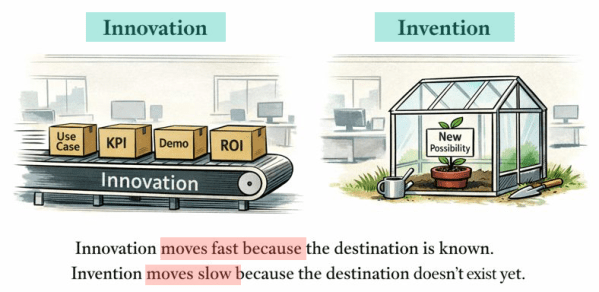
The post discusses how the current focus on fast, outcome-driven innovation in the GenAI landscape risks sidelining invention, which nurtures genuine new possibilities. It emphasizes that while innovation thrives in KPI-oriented settings, invention often struggles for justification. The author calls for a deliberate balance to preserve the space for invention in future developments.
A Music AI Video Generation: Run Local, Offline, and Free on macOS
This post outlines how music creators can run AI image and video generation locally on Mac with Apple Silicon, emphasizing offline use without subscriptions. It details the setup process, focusing on generating visuals for music projects through ComfyUI, Stable Diffusion, and Stable Video Diffusion, ensuring complete user control over their creative workflows.
RAG is Dead … Long Live RAG
The post explains why traditional Retrieval-Augmented Generation (RAG) approaches no longer scale and how modern architectures, including GraphRAG, address these limitations. It highlights why data quality, metadata, and disciplined system design matter more than models or frameworks, and provides a practical foundation for building robust RAG systems, illustrated with IBM technologies but applicable far beyond them.
AI-Generated Software, Patents, and Global IP Law — A First Deep Dive using AI
The content explores the evolving role of AI in creative processes and its implications for intellectual property (IP) law. It highlights challenges around ownership, patentability, and copyright concerning AI-generated works. As AI advances, existing legal frameworks struggle to keep pace, prompting questions about creativity, innovation, and the need for new regulations.
Update Ollama to use Granite 4 in VS Code with watsonx Code Assistant
This post is about setup to utilize Granite 4 models in Ollama for VS Code with watsonx Code Assistant. The process includes inspecting available models, uninstalling old versions, installing new models, and configuring them for effective use. The experience emphasizes exploration and learning in a private, efficient AI development environment.
Access watsonx Orchestrate functionality over an MCP server
The Model Context Protocol (MCP) is being increasingly utilized in AI applications, particularly with the watsonx Orchestrate ADK. This setup allows users to develop and manage agents and tools through a seamless integration of the MCP server and the Development Edition, enhancing user interaction and functionality in coding environments.
It’s All About Risk-Taking: Why “Trustworthy” Beats “Deterministic” in the Era of Agentic AI
This post explores how Generative AI and Agentic AI emphasize trustworthiness over absolute determinism. As AI's role in enterprises evolves, organizations must focus on building reliable systems that operate under risk, balancing innovation with accountability. A personal perspective.
Integrating watsonx Orchestrate Agent Chat in Web Apps
This blog post demonstrates the usage of the web channel functionality in watsonx Orchestrate, enabling the embedding of conversational AI agents into custom web applications. It guides users through setting up a remote environment, generating source code, and running a web server to invoke chat features, emphasizing ease of use and customization options.
Avoid the DCO error for your pull requests in a GitHub repository fork
The content provides a solution for resolving the 'DCO is missing' error encountered when forking a GitHub project. It outlines steps to amend commits with sign-off, including adding a commit-msg hook script. Successfully following these instructions helps ensure that your pull request functions correctly.
Getting Started with Local AI Agents in the watsonx Orchestrate Development Edition
The blog post outlines the process of setting up the Agent Developer Kit (ADK) to build and run AI agents locally using WatsonX Orchestrate Developer Edition. It involves setting up prerequisites, installing the necessary software, and loading an example agent—optional integration with Langfuse for observability.