This short blog post is about my perspective related to, how to get technical started with white box security testing, when you use SonarQube.
I want to start with an introduction from one of my last blog posts:
“I like the OWASP Top Ten for “developers” charts. From my point of view, it gives an awesome advice, where to start and helps to take care and remember, what you maybe already know about web security implementation. From my side it feels a bit like “rub salt into the wound” of a developer soul, isn’t it so?”
During the inspection of the Cloud Native ToolkitCloud Native Toolkit.
I noticed that SonarQube highlights that its closely related to the OWASP top ten, that sounds awesome.
A bit about SonarQube
Here is a statement from SonarQube‘s website.
“OWASP Top 10 – We’ve got you covered! See issues in the 10 most critical security risk categories in your web applications.”
SonarQube comes in four different versions as you see on their download page.
- Community Edition Free/Open-Source Edition – The starting point for adopting code quality in your CI/CD.
- Developer Edition – Maximum Application Security; Maximum value across branches & PRs
- Enterprise Edition – Manage your Application Portfolio, enable Code Quality & Security at an Enterprise level.
- Data Center Edition – High Availability, for global deployments.
I followed their awesome easy get started 2 minutes documentation for SonarQube, they just using a simple Docker image.
It’s really incredible fast, how you are able to start with security and code quality scanning for your project, with this nonproductive Docker image. When you scan your Java Maven projects, it’s really amazing fast and you really have only 2 min until you can run your first report. With JavaScript it takes a bit longer.
Example to start scanning of a JavaScript project on MacOS¶
When you want to start with JavaScript it takes a bit longer, here is an example how I started.
In that situation you have to run two container images and you have to add the sonarqube-project.properties file to your source code project:
- SonarQube server container – contains the analysis results
- SonarQube scanner container – doing the scanning
- SonarQube project configuration file for your source code
Let’s start with the steps I did:
Step 1: Start the SonarQube server
docker run -d --name sonarqube -e SONAR_ES_BOOTSTRAP_CHECKS_DISABLE=true -p 9000:9000 sonarqube:latest
Step 2: Add a sonarqube-project.properties file into your source code project.
This is the configuration I used for my example.
# must be unique in a given SonarQube instance
sonar.projectKey=sample
# --- optional properties ---
# defaults to project key
sonar.projectName=sample
# defaults to 'not provided'
#sonar.projectVersion=1.0
# Path is relative to the sonar-project.properties file. Defaults to .
sonar.sources=.
# Encoding of the source code. Default is default system encoding
sonar.sourceEncoding=UTF-8
Step 3: Run the sonarqube scanner container
Start the sonarqube scanner container for your source code project. (ensure you use –network=host )
export SONARQUBE_URL=localhost:9000
export MYTOKEN=YOUR_TOKEN
export YOUR_REPO=/YOUR_PATH_TO_THE_SOURCE_CODE
docker run \
--network=host \
--rm \
-e SONAR_HOST_URL="http://${SONARQUBE_URL}" \
-e SONAR_LOGIN="$MYTOKEN" \
-v "${YOUR_REPO}:/usr/src" \
sonarsource/sonar-scanner-cli
Step 4: Examine your results in the sonarqube server
Example overall result:
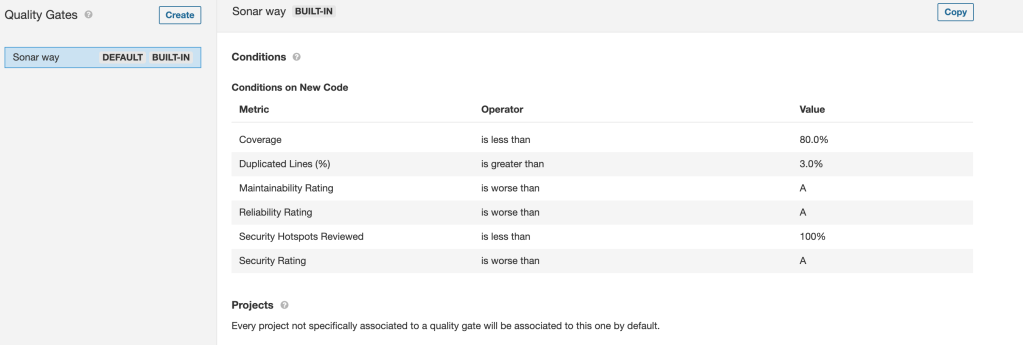
- Predefined Quality Gates
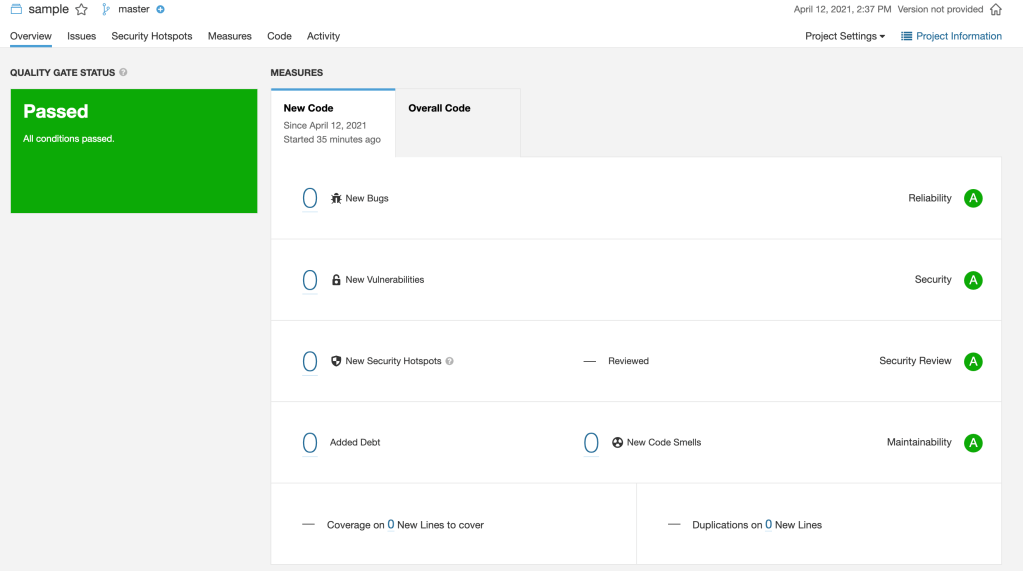
- Project overview
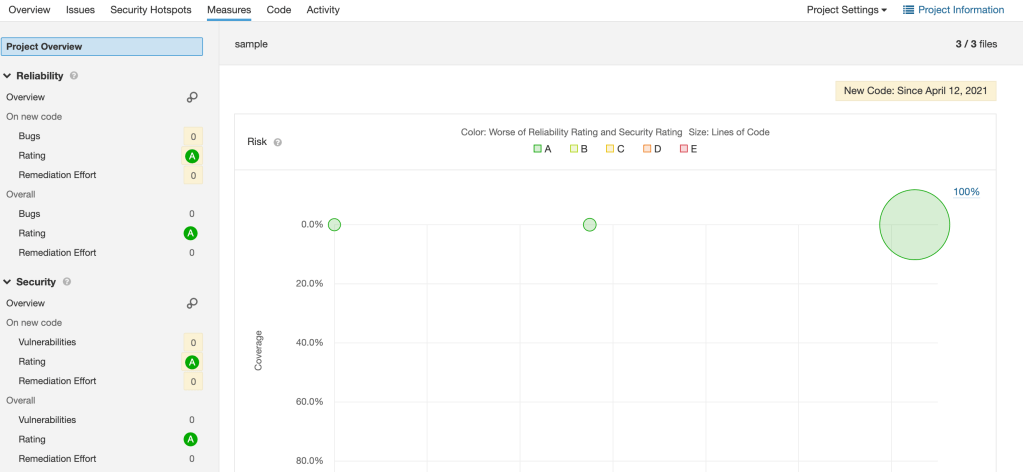
- Project overview related to Reliability and Security
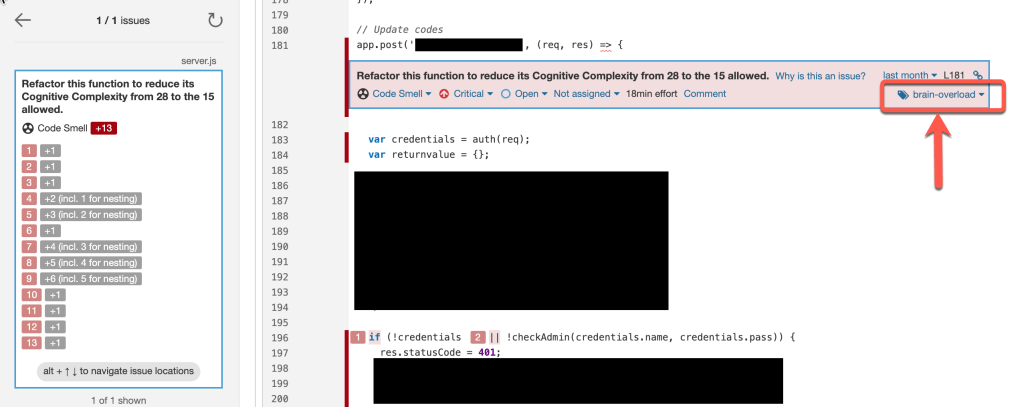
For example you get an information like the tag brain-overload, which shows you maybe have written to complex code.
Summary¶
When I started to inspect the OWASP Top Ten for “developers” charts I noticed there is a lot to know and learn. So know I am happy that the Cloud Native Toolkit guided me to the right open-source direction to get an incredible technical fast start for security and quality scanning of source code.
From my point of view, I would say after reading this short blog post, you can’t no longer say, that you didn’t know how to get started with security scanning at low cost from a technical point of view. 😉 With SonarQube you get an incredible technical fast start for security and quality scanning for your source code, even when I know this is only about the starting point and not about the deep dive.
I hope this was useful for you and let’s see what’s next?
Greetings,
Thomas
#security, #sonarqube, #javascript, #owasp


Leave a comment