This blog post is about automating the creation of a Red Hat OpenShift cluster on IBM Cloud in a Virtual Private Cloud. I used bash scripting with the IBM Cloud CLI and and the associated IBM Cloud CLI plugins vpc-infrastructure and kubernetes-service. I also use jq to handle json output.
I created the bash automation in combination of the IBM Cloud documentation and tutorials and my blog post about the automated setup of a simple Virtual Private Cloud. It’s more about learning and not so much for production.
These are the three resources I used in the IBM Cloud documentation:
- Creating Red Hat OpenShift on IBM Cloud clusters (Classic)
- Creating an OpenShift cluster in your Virtual Private Cloud (VPC)
- OpenShift and Kubernetes CLI
I’m not going to show every function of the bash script in this blog post. For details, please visit the script in the GitHub project.
The automation
The main steps in script execution are:
- Create a
Virtual Private Cloud. - Rename the automated created elements of the
Virtual Private Cloud. - Create a
Public Gatewayin theVirtual Private cloudand attach it to theSubnetyou plan to use. - Create the
Cloud Object Storage. - Create the
Red Hat OpenShift cluster
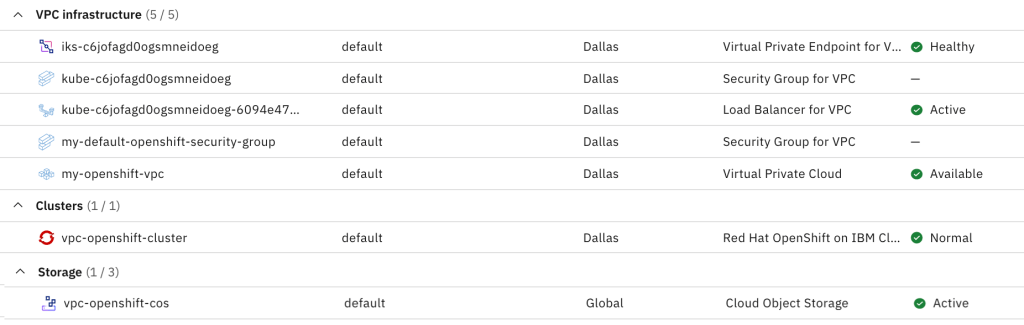
The image below shows an example of the resources you will notice in your IBM Cloud web UI resource list after you run the script.
The simplified architecture
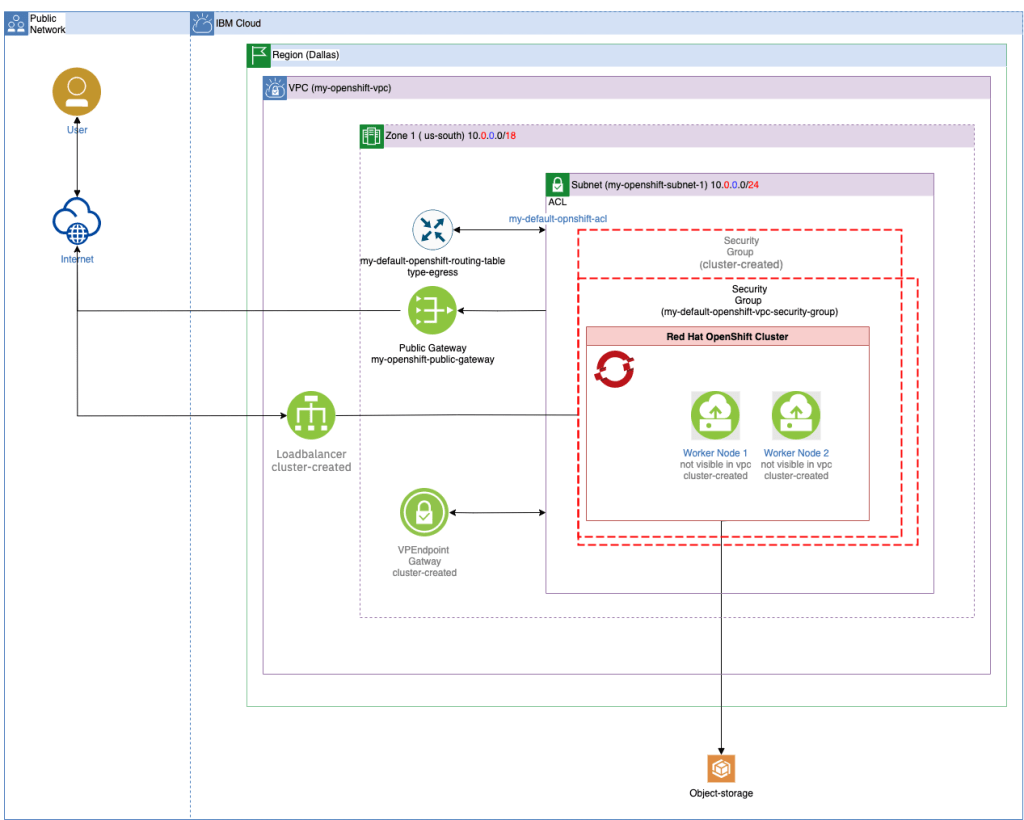
The following architecture diagram shows a simplified architecture with all of the resources we created and their high-level dependencies. For more information, see the great IBM Cloud documentation I listed at the beginning.
By default, the script creates the vpc resources and cluster in the Dallas region and uses the default resource group as you can verify in the image above. The cloud object storage is set up globally and is also a part of the resource group default. The elements within the diagram that contain the information cluster created are those resources that are automatically created when the cluster is created. Not visible in VPC only means that you can’t access the virtual server instances (VSI) for the worker nodes, but you can see them in the IBM Cloud web UI for the cluster itself.
Note: The starting point for the diagram you find in the templates of draw.io for IBM Cloud. (optional additional icons)
This is an animated version of the simplified architecture diagram and shows the steps of the automation.

Execute the script automation in the IBM Cloud Shell¶
- Step 1:Open the IBM Cloud Shell in from your IBM Cloud Web UI
- Step 2: Clone the GitHub project into the IBM Cloud Shell
git clone https://github.com/thomassuedbroecker/simple-vpc-ibm-cloud.git
- Step 3: Open the project folder
cd simple-vpc-ibm-cloud
- Step 4: Checkout the needed GitHub project branch
git checkout setup-vpc-openshift
- Step 5: Open the scripts folder
cd scripts
- Step 6: Log on to IBM Cloud
ibmcloud login [--sso]
- Step 7: Create an environment file and adjust the variables to your needs.
cat .env_template > .env
- Step 8: Execute the bash script
bash create-openshift-on-vpc.sh
- Step 9: Note the steps outlined in the script and press Enter to continue.
- Step 10: When the cluster is created, a browser window will open so you can see the current status of the cluster creation.
- Step 11: When your Red Hat OpenShift cluster on the IBM Cloud is ready, open the Red Hat web console from the IBM Cloud web UI you are currently in.
- Step 12: Done
Summary
There are several ways to automate the setup, there is also the option to do this with Terraform, but in my case I used traditional bash script automation with CLI and the plugins of the IBM Cloud.
The IBM Cloud documentation for this automation build is great, and I’ve provided you with the links for an easy entry point if you want to dig deeper into this topic.
I hope this was useful for you and let’s see what’s next?
Greetings,
Thomas
PS: Here is an useful link to an automated creation of a Red Hat OpenShift cluster on IBM Cloud with the Cloud Native Toolkit. Here you find some Terraform modules at this link https://modules.cloudnativetoolkit.dev/ . This is my related blog post to the topics: Start with CICD using the Cloud Native Toolkit from the IBM Garage.
In addition maybe this is also useful “Architecture and Security Controls Enterprise Tool” (ASCET) https://ascent.openfn.co.
“ASCENT is a tool created by IBM to accelerate partner’s journey to the IBM Cloud. Through automation and integration, ASCENT enables enterprises to deliver compliant cloud architectures which can be clearly evidenced and communicated with Governance, Risk and Compliance teams. Click on the links below to learn more about how ASCENT automates and integrates Security Controls, Reference Architectures and Cloud Services.” source https://ascent.openfn.co
#ibmcloud, #roks, #vpc, #openshift, #automation. #ibmdeveloper

